Matt Gorham is a Partner and US Cyber & Privacy Innovation Institute Leader, Barbara Berlin is a Managing Director at the Governance Insights Center, and Kevin Vaughn is a Partner at the National Office at PricewaterhouseCoopers LLP. This post is based on their PwC memorandum.
The Securities and Exchange Commission (SEC) released its final rule on Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure on July 26, 2023. This gives your organization approximately five months to confirm your compliance plans before the new disclosure requirements take effect in mid-December.
The revisions from the proposed rule have streamlined the disclosure requirements in many ways, in response to more than 150 comment letters filed from issuers, investors, and other parties.
Still, disclosure can seem a daunting prospect if your company’s cybersecurity program won’t withstand investor scrutiny. Many companies are not ready today to reveal their cyber capabilities to the extent that the new rule requires. Note that final rules require the cybersecurity disclosures to be presented in Inline eXtensible Business Reporting Language (“Inline XBRL”).
Many companies will focus on enhancing their cybersecurity capabilities as they plan for the new disclosure requirements
The disclosure requirements aim to protect investors from the harms that a cybersecurity breach could cause. As the number, severity, and stakes of cybersecurity incidents continue to rise, investors are demanding transparency from the companies in which they’ve placed their resources and trust.
With this new rule, the SEC puts the onus on companies to give investors current, consistent and “decision-useful” information about how they manage their cyber risks.
We see the rule as a call to action, challenging enterprises to be ready to expand their disclosures regarding their cyber risk management, strategy, and governance processes. For some, preparing to reveal this information will not be easy. But it might not be as difficult as you might think.
Requirement for transparency into cyber practices and incidents has shifted from statutory to actionable, from inconsistent and incomplete to “decision-useful.”
The new rule: what it says, who’s responsible
The final rule requires that, in annual 10-K filings, companies add details describing their cyber program.
It also requires mandatory and speedier filing of Form 8-K for reporting material cybersecurity incidents to the SEC when they occur — within four days of determining that an incident is material. In the rule, cyber incident means an unauthorized occurrence (or series of related occurrences) on or conducted through a registrant’s information systems that jeopardizes the confidentiality, integrity, or availability of a registrant’s information systems or any information residing therein.
The rule provides for a series of extensions if the US Attorney General determines that immediate disclosure would pose a substantial risk to national security or public safety.
For more details on the rule, see our In brief, SEC adopts cybersecurity disclosure rule.
In a nutshell
SEC’s disclosure requirements for public companies
Cyber incident reporting
Report “material” cybersecurity incidents on a Form 8-K within four business days of materiality determination.
Describe the nature, scope, and timing of the incident and the material impact or reasonably likely material impact on the registrant. To the extent required information is not determined or is unavailable at the time of the filing, the 8-K should include disclosure of this fact, and the 8-K should be later amended when the information is determined or becomes available.
Materiality determination should be based on federal securities law materiality, including consideration of quantitative and qualitative factors.
Cyber risk management and strategy
Describe the company’s process, if any, for assessing, identifying, and managing material risks from cybersecurity threats, including:
- whether cybersecurity is part of the overall risk management program, engages consultants, auditors or other third parties, and processes to oversee and identify risks from use of third-parties.
- whether and how any risks from cybersecurity threats have materially affected or are reasonably likely to materially affect the registrant’s business strategy, results of operations, or financial condition.
Cyber governance
Describe the company’s governance of cybersecurity risks as it relates to:
The board’s oversight of cybersecurity risk, including identification of any board committee or subcommittee responsible for oversight and the process by which they are informed about cyber risks.
Management’s role and expertise in assessing and managing material cybersecurity risk and implementing cybersecurity policies, procedures and strategies.
Specific disclosure of any management positions or committees responsible for assessing and managing cyber risks, including discussion of their relevant expertise.
Effectivity dates: The material incident disclosure requirements would be effective on or after December 18, 2023 (smaller reporting companies have a 180-day deferral). Disclosures for risk management, strategy and governance would be effective for all registrants for fiscal years ending on or after December 15, 2023.
At most companies, responsibility for compliance will rest among those in several primary roles, each with their own questions to ponder.
Organizations that don’t comply with the new rule will likely face serious consequences, as recent SEC enforcement actions suggest. The Commission has levied large fines against companies for not disclosing breaches sufficiently or in a timely manner. It continues a two-pronged approach to enforcement: first, that organizations have appropriate disclosures under the requirements, and second, that they have controls and procedures in place to escalate necessary items for determination of whether disclosures are required.
CEO or CFO
When I sign and certify my company’s 10-K, am I confident in the integrity and completeness and accuracy of the information the company is disclosing related to the cyber risk management program? Are we prepared to make the expanded disclosures the new rule requires?
Boards
Are we getting the effective, ongoing reporting we need to understand the key cyber risks and what management is doing to mitigate those risks? How do we know we’re asking the right questions of the CISO and others who report to us? Are we comfortable with our own cybersecurity knowledge to effectively oversee this area?
CIO/CISO and team
Are the details of my cyber risk management program sufficient to disclose to investors to the extent required by the SEC’s expanded disclosure requirements? How much do we disclose without introducing additional risk to the company?
How will we make sure that the people responsible for determining the materiality of a cybersecurity incident have the information they need to make that determination without unreasonable delay? If an incident is material, how do we confirm that required information is included in the filed 8-K within the SEC’s four-day window?
Legal
How effectively can we draft disclosures to the SEC in a way that is compliant yet doesn’t give away confidential information about the organization’s cyber program? Which criteria and considerations should we use to help determine (with the CISO and those responsible for SEC reporting) whether or not an incident qualifies as “material”?
If the immediate disclosure of the incident potentially poses a substantial risk to public safety or national security, how do we report it to federal law enforcement and confirm we are well coordinated internally? How will we be informed of any determinations and communications made to the SEC that could affect the required timing for our reporting?
Internal audit
What is our role in confirming that disclosures are complete, accurate and sound?
The full view
Complying with the new rule will require coordination among security, finance, risk and legal teams, as well as, key business leaders (when needed). So it’s helpful to agree internally on how to make timely and accurate disclosures that satisfy the SEC ruling.
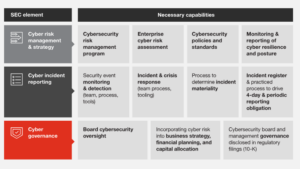
The good news is that these capabilities are mutually-reinforcing: improving one area will also help you improve in other areas. Here’s a helpful framework for unifying your organizational efforts.
The capabilities you need for decision-useful reporting on your cyber strategy and practices
A PwC framework
Eight questions to answer for SEC cyber disclosure success
Since the proposal’s initial publication, some questions have arisen repeatedly in our conversations with board members, CFOs, CIOs, and CISOs. Companies need to answer these questions clearly to pass muster with the SEC and investors.
Cyber incident disclosures
1. What is our process for reporting cybersecurity incidents? It’s important for leaders and the board to understand the internal escalation and external reporting processes. Consider testing the escalation process now, before an event occurs.
2. How can we effectively determine materiality of a breach or attack? Determining materiality can be complex and should not be solely the responsibility of any one person. Materiality determinations should involve the CFO, General Counsel, CISO, CIO, and front-line business leaders.
Organizations will already have heeded guidance the SEC released in 2018 regarding cyber disclosures, and will have disclosure controls and procedures that “provide an appropriate method of discerning the impact … on the company and its business, financial condition, and results of operations, as well as a protocol to determine the potential materiality of such risks and incidents.”
Many organizations are already comfortable discussing materiality in terms of financial statements, but the discussion doesn’t stop there. You also need to consider qualitative factors, such as effects on reputation, customer relationships, vendor relationships and regulatory compliance. And you’ll need to begin taking a long view of breaches and breach attempts, considering cumulative effects of related occurrences.
3. How do we confirm that our processes for determining materiality are thoroughly documented? When incidents arise, you’ll want to have documentation detailing how you determined the materiality of an incident, particularly if you determine it’s not material. If the SEC questions your conclusion, you’ll need to justify with details of your processes and considerations of quantitative and qualitative factors, and the rationale and basis for your decision.
4. What is the right level of information to disclose? Recognizing the sensitivity of cybersecurity programs, the SEC’s disclosures are generally more principles-based. Nonetheless, complying with the new requirements without revealing confidential information about your cybersecurity procedures and program will be an important consideration. Some companies are creating a standard template for reporting incidents to have on hand, then modify should an event occur.
5. Can we report within the four-day period? We see a lot of confusion surrounding the four-day timeframe for disclosing an incident. The clock starts ticking not when the incident occurs or is detected, but when it is determined to be “material.” The rule does not set forth any specific timeline between the incident and the materiality determination, but the materiality determination should be made without unreasonable delay.
6. How will we comply with the requirement to report related occurrences that qualify as “material”? The final rule removed the requirement to aggregate disparate non-material risks to determine if a 8-K disclosure is required. However, the final rule still requires events that are related — for example, the same malicious actor or that exploit the same vulnerability — to be reported if a company determines they’re material.
Cyber risk management and strategy
7. Are our organization’s policies and procedures, risk assessments, controls and controls monitoring strong enough to disclose publicly?
Policies and procedures: Are yours in line with the specifications in at least one recognized industry framework? Are they updated regularly? Does everyone in the organization know what they are, and how they are responsible for following them? Are they well enforced?
Risk assessment: Having a risk assessment process is not enough. Is yours robust? Is it applied throughout the organization, focusing on top risks to the business? How often do you do risk assessments? Are assessment results incorporated into your enterprise cyber strategy, enterprise risk management program and capital allocations? Have you engaged a third party to assess our cybersecurity program?
Controls and controls monitoring: How does your organization monitor the effectiveness of its risk mitigation activities and controls? How mature are your capabilities, as evaluated against an industry framework? How are leadership and the board informed about the effectiveness of these controls?
Cyber governance and reporting
8. Are we getting the information we need to oversee cybersecurity at the board level? The final rule requires a description of the board’s oversight of cybersecurity risks in the 10-K. This could include where cybersecurity risk is allocated (e.g., full board, committee) and the processes by which the board/committee is informed about the risks.
While the final rules no longer require disclosure of cyber expertise, directors should consider how comfortable they are in the areas that the rule specifies. As a whole, boards are responsible for understanding cyber concepts and requirements well enough to provide oversight. How will directors individually and collectively confirm that they continue to learn? Will they invite cyber experts to meetings? Will they attend classes or other kinds of training? Will they consult with outside advisors?
Assess and test your preparedness
Is your cyber program disclosure-ready? Test your answers to the questions above. A thorough diagnostic overview of these findings can show you precisely where you need to make changes, to satisfy investors and the public that you are protecting company assets and the company’s reputation.
You may also wish to schedule a “tabletop” exercise in which you and your team enact the processes that you will employ in the event of a cybersecurity incident — to include the process for determining materiality and providing the information required by the 8-K within four business days of the materiality determination. If you’re not confident that you’re ready to make these disclosures properly or in a timely manner, then this sort of exercise will help you get there. If you do feel confident, then a tabletop can validate your conviction — or raise flags that you might not have seen otherwise.
Clients who’ve run these assessment diagnostics and preparedness exercises often find, to their surprise, that they’re not as ready for the new SEC disclosures as they thought. Taking these steps now can help you avoid unpleasant surprises later: not only SEC fines, but also loss of investor confidence and trust and market value.
 Print
Print